Микротик что такое bridge
Объясните, зачем нужен Bridge в Mikrotik?
Зарегистрирован: 13.08.2008
Пользователь #: 70,537
Сообщения: 315

Житель sysadmins
Зарегистрирован: 22.01.2016
Пользователь #: 160,064
Сообщения: 9205
Зарегистрирован: 19.05.2010
Пользователь #: 87,707
Сообщения: 286
Зарегистрирован: 22.01.2016
Пользователь #: 160,064
Сообщения: 9205
Зарегистрирован: 13.08.2008
Пользователь #: 70,537
Сообщения: 315
Зарегистрирован: 13.08.2008
Пользователь #: 70,537
Сообщения: 315
Зарегистрирован: 13.08.2008
Пользователь #: 70,537
Сообщения: 315
Зарегистрирован: 13.08.2008
Пользователь #: 70,537
Сообщения: 315
Зарегистрирован: 22.01.2016
Пользователь #: 160,064
Сообщения: 9205
Зарегистрирован: 13.08.2008
Пользователь #: 70,537
Сообщения: 315
Стоит заметить, что существует не один способ организации VLAN трафика на Mikrotik. Но только один из этих способов конфигурации VLAN является наиболее корректным, позволяющим исключить проблемы с производительностью и подключением.
Начиная с версии RouterOS 6.41 стало возможно использовать мост для фильтрации VLAN и именно эта конфигурация рекомендована официальным Wiki Mikrotik.
Освоить MikroTik Вы можете с помощью онлайн-куса « Настройка оборудования MikroTik ». Курс основан на официальной программе MTCNA. Автор курса – официальный тренер MikroTik. Подходит и тем, кто уже давно работает с микротиками, и тем, кто еще их не держал в руках. В курс входит 162 видеоурока, 45 лабораторных работ, вопросы для самопроверки и конспект.
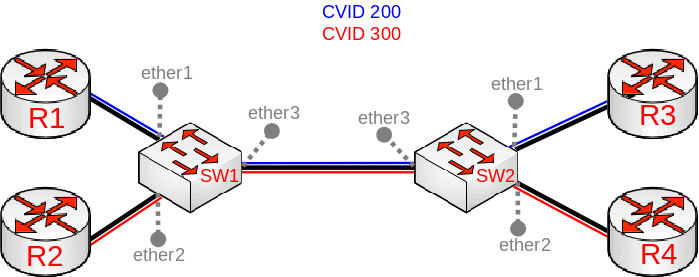
Рассмотрим базовую конфигурацию VLAN позволяющую разделить локальную сеть на два виртуальных сегмента для разных отделов офиса.
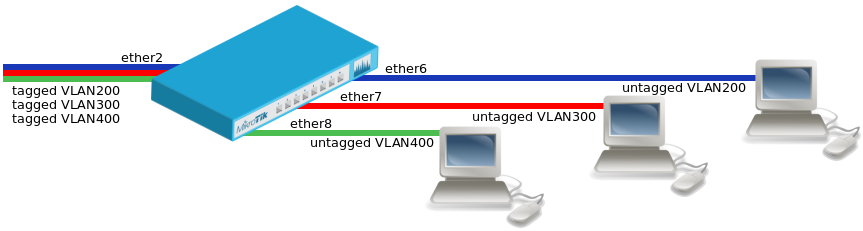
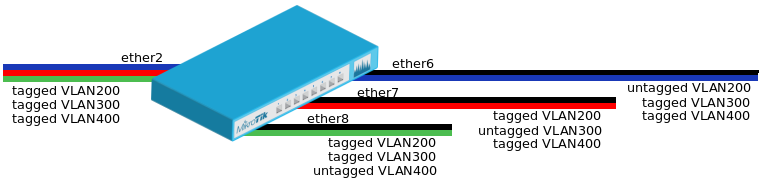
Базовая схема коммутации VLAN
Для начала нам необходимо создать мост bidge1 с фильтрацией VLAN. Для включение фильтрации VLAN перейдите во вкладку VLAN и отметьте пункт «VLAN Filtering».
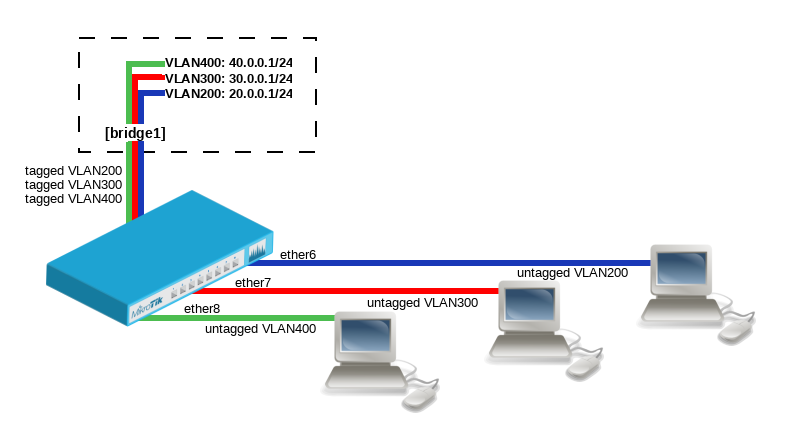
Мост с фильтрацией VLAN
В статье я буду приводить примеры настроек как для графического интерфейса так и для консоли.
Добавляем порты в мост bidge1 и назначаем им PVID.
Добавление access порта с PVID в bridge
Добавляем соответствующие записи в VLAN таблицу моста.
VLAN таблица моста
В случае работающей VLAN фильтрации на bridge таблица VLAN выглядит примерно так:
Освоить MikroTik Вы можете с помощью онлайн-куса « Настройка оборудования MikroTik ». Курс основан на официальной программе MTCNA. Автор курса – официальный тренер MikroTik. Подходит и тем, кто уже давно работает с микротиками, и тем, кто еще их не держал в руках. В курс входит 162 видеоурока, 45 лабораторных работ, вопросы для самопроверки и конспект.
Всё гениально и просто.
Спасибо кеп!
Подскажите пожалуйста, в некоторых мануалах видел, что на этапе добавления записей в таблицу VLAN добавляют помимо портов еще и бридж, в каких случаях это нужно делать, а в каких нет?
Если вы повесите vlan на бридж, то он будет доступен на всех интерфейсах (портах) входящих в этот бридж, вот и все.
вопрос был не про vlan в бридж, а бридж во vlan, например в поле tagged, а делаю это для того, чтобы vlan имел доступ к процессору роутера, так как бридж по сути является портом cpu, и если не добавить бридж в вилан, то из этого вила не будет доступно, например, управление роутером.
Не понимаю о чем вы, что за доступ к процессору и порты cpu? Бридж не может быть никаким портом cpu! Если вы работаете с vlan, то вам нужно для начала понять что это такое, разобраться в понятиях trunk и access порта. И тогда больше не будете терять доступ к управлению микротиком.
Если вы хотите в порт микротика отправлять vlan и при этом чтобы подключенный на этот порт клиент работал без vlan (не умеет работать с vlan), то вам нужен access порт.
Не надо создавать фильтрацию vlan на существующем бридже, через который осуществляется управление микротиком. Здесь ключевое слово СОЗДАТЬ мост.
У вас по записям и по картинкам как раз и управление и фильтрация на одном бридже bidge1
Manual:Interface/Bridge
Applies to RouterOS: v3, v4+
Contents
Summary
Ethernet-like networks (Ethernet, Ethernet over IP, IEEE 802.11 in ap-bridge or bridge mode, WDS, VLAN) can be connected together using MAC bridges. The bridge feature allows the interconnection of hosts connected to separate LANs (using EoIP, geographically distributed networks can be bridged as well if any kind of IP network interconnection exists between them) as if they were attached to a single LAN. As bridges are transparent, they do not appear in traceroute list, and no utility can make a distinction between a host working in one LAN and a host working in another LAN if these LANs are bridged (depending on the way the LANs are interconnected, latency and data rate between hosts may vary).
Bridge Interface Setup
Sub-menu: /interface bridge
To combine a number of networks into one bridge, a bridge interface should be created (later, all the desired interfaces should be set up as its ports). One MAC address from slave (secondary) ports will be assigned to the bridge interface, the MAC address will be chosen automatically, depending on «port-number», and it can change after a reboot. To avoid unwanted MAC address changes, it is recommended to disable «auto-mac», and to manually specify MAC by using «admin-mac».
Properties
Example
To add and enable a bridge interface that will forward all the protocols:
Spanning Tree Protocol
RouterOS bridge interfaces are capable of running Spanning Tree Protocol to ensure a loop-free and redundant topology. For small networks with just 2 bridges STP does not bring much benefits, but for larger networks properly configured STP is very crucial, leaving STP related values to default may result in completely unreachable network in case of a even single bridge failure. To achieve a proper loop-free and redundant topology, it is necessary to properly set bridge priorities, port path costs and port priorities.
Warning: In RouterOS it is possible to set any value for bridge priority between 0 and 65535, the IEEE 802.1W standard states that the bridge priority must be in steps of 4096. This can cause incompatibility issues between devices that does not support such values. To avoid compatibility issues, it is recommended to use only these priorities: 0, 4096, 8192, 12288, 16384, 20480, 24576, 28672, 32768, 36864, 40960, 45056, 49152, 53248, 57344, 61440
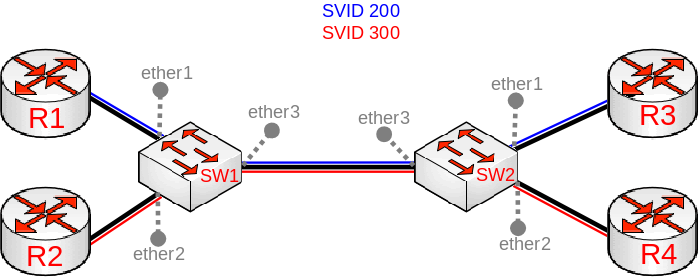
STP has multiple variants, currently RouterOS supports STP, RSTP and MSTP. Depending on needs, either one of them can be used, some devices are able to run some of these protocols using hardware offloading, detailed information about which device support it can be found in the Hardware Offloading section. STP is considered to be outdated and slow, it has been almost entirely replaced in all network topologies by RSTP, which is backwards compatible with STP. For network topologies that depend on VLANs, it is recommended to use MSTP since it is a VLAN aware protocol and gives the ability to do load balancing per VLAN groups. There are a lot of considerations that should be made when designing a STP enabled network, more detailed case studies can be found in the Spanning Tree Protocol section. In RouterOS the protocol-mode property controls the used STP variant.
Note: By the IEEE 802.1ad standard the BPDUs from bridges that comply with IEEE 802.1Q are not compatible with IEEE 802.1ad bridges, this means that the same bridge VLAN protocol should be used across all bridges in a single Layer2 domain, otherwise (R/M)STP will not function properly.
Per port STP
There might be certain situations where you want to limit STP functionality on a single or multiple ports. Below you can find some examples for different use cases.
Warning: Be careful when changing the default (R/M)STP functionality, make sure you understand the working principles of STP and BPDUs. Misconfigured (R/M)STP can cause unexpected behaviour.
In this example BPDUs will not be sent out through ether1. In case the bridge is the root bridge, then loop detection will not work on this port. If another bridge is connected to ether1, then the other bridge will not receive any BPDUs and therefore might become as a second root bridge. You might want to consider blocking received BPDUs as well.
Note: You can use Interface Lists to specify multiple interfaces.
In this example all received BPDUs on ether1 are dropped. This will prevent other bridges on that port becoming a root bridge.
Warning: If you intend to drop received BPDUs on a port, then make sure to prevent BPDUs from being sent out from the interface that this port is connected to. A root bridge always sends out BPDUs and under normal conditions is waiting for a more superior BPDU (from a bridge with a lower bridge ID), but the bridge must temporarily disable the new root-port when transitioning from a root bridge to designated bridge. If you have blocked BPDUs only on one side, then a port will flap continuously.
In this example if ether1 receives a BPDU, it will block the port and will require you to manually re-enable it.
Bridge Settings
Sub-menu: /interface bridge settings
Note: In case you want to assign Simple Queues (Simple QoS) or global Queue Trees to traffic that is being forwarded by a bridge, then you need to enable the use-ip-firewall property. Without using this property the bridge traffic will never reach the postrouting chain, Simple Queues and global Queue Trees are working in the postrouting chain. To assign Simple Queues or global Queue Trees for VLAN or PPPoE traffic in a bridge you should enable appropriate properties as well.
Port Settings
Sub-menu: /interface bridge port
Port submenu is used to enslave interfaces in a particular bridge interface.
Example
To group ether1 and ether2 in the already created bridge1 bridge
Interface lists
Starting with RouterOS v6.41 it possible to add interface lists as a bridge port and sort them. Interface lists are useful for creating simpler firewall rules, you can read more about interface lists at the Interface List section. Below is an example how to add interface list to a bridge:
Ports from a interface list added to a bridge will show up as dynamic ports:
It is also possible to sort the order of lists in which they appear in the /interface bridge port menu. This can be done using the move command. Below is an example how to sort interface lists:
Note: The second parameter when moving interface lists is considered as «before id», the second parameter specifies before which interface list should be the selected interface list moved. When moving first interface list in place of the second interface list, then the command will have no effect since the first list will be moved before the second list, which is the current state either way.
Hosts Table
MAC addresses that have been learned on a bridge interface can be viewed in the /interface bridge host menu. Below is a table of parameters and flags that can be viewed.
Sub-menu: /interface bridge host
| Property | Description |
|---|---|
| age (read-only: time) | The time since the last packet was received from the host. Appears only for dynamic, non-external and non-local host entries |
| bridge (read-only: name) | The bridge the entry belongs to |
| disabled (read-only: flag) | Whether the static host entry is disabled |
| dynamic (read-only: flag) | Whether the host has been dynamically created |
| external (read-only: flag) | Whether the host has been learned using an external table, for example, from a switch chip or Wireless registration table. Adding a static host entry on a hardware-offloaded bridge port will also display an active external flag |
| invalid (read-only: flag) | Whether the host entry is invalid, can appear for statically configured hosts on already removed interface |
| local (read-only: flag) | Whether the host entry is created from the bridge itself (that way all local interfaces are shown) |
| mac-address (read-only: MAC address) | Host’s MAC address |
| on-interface (read-only: name) | Which of the bridged interfaces the host is connected to |
Monitoring
To get the active hosts table:
Static entries
Since RouterOS v6.42 it is possible to add a static MAC address entry into the hosts table. This can be used to forward a certain type of traffic through a specific port. Another use case for static host entries is for protecting the device resources by disabling the dynamic learning and rely only on configured static host entries. Below is a table of possible parameters that can be set when adding a static MAC address entry into the hosts table.
Sub-menu: /interface bridge host
| Property | Description |
|---|---|
| bridge (name; Default: none) | The bridge interface to which the MAC address is going to be assigned to. |
| disabled (yes | no; Default: no) | Disables/enables static MAC address entry. |
| interface (name; Default: none) | Name of the interface. |
| mac-address (MAC address; Default: ) | MAC address that will be added to the hosts table statically. |
| vid (integer: 1..4094; Default: ) | VLAN ID for the statically added MAC address entry. |
For example, if it was required that all traffic destined to 4C:5E:0C:4D:12:43 is forwarded only through ether2, then the following commands can be used:
Bridge Monitoring
Sub-menu: /interface bridge monitor
Used to monitor the current status of a bridge.
| Property | Description |
|---|---|
| current-mac-address (MAC address) | Current MAC address of the bridge |
| designated-port-count (integer) | Number of designated bridge ports |
| port-count (integer) | Number of the bridge ports |
| root-bridge (yes | no) | Shows whether bridge is the root bridge of the spanning tree |
| root-bridge-id (text) | The root bridge ID, which is in form of bridge-priority.bridge-MAC-address |
| root-path-cost (integer) | The total cost of the path to the root-bridge |
| root-port (name) | Port to which the root bridge is connected to |
| state (enabled | disabled) | State of the bridge |
Example
To monitor a bridge:
Bridge Port Monitoring
Sub-menu: /interface bridge port monitor
Statistics of an interface that belongs to a bridge.